The Surprising Link Between Employee and Business Security

When you think about cybersecurity, what comes to mind? Firewalls, antivirus software, and complex encryption probably top the list. While these technological defenses are essential, the surprising truth is that your company’s biggest vulnerability isn’t a piece of hardware or software. It’s the people who use it every day.
If this feels unsettling, you’re not alone. In fact, three in four (74%) CISOs consider human error to be their top cybersecurity risk. Your employees are unintentionally your greatest vulnerability, but here’s the crucial takeaway: with the right strategy, they can become your strongest line of defense.
This guide provides a clear, actionable framework for transforming your team from a potential liability into a proactive security asset. We’ll move beyond the problem and give you the tools to build a resilient, security-conscious organization from the ground up.
Key Takeaways
- Human error is a significant factor in the vast majority of data breaches, making employee awareness a critical business priority for mitigating risk.
- Building a “human firewall” relies on three core pillars: a clear and simple policy, comprehensive and ongoing training on common threats like phishing, and a culture of continuous reinforcement.
- A successful cybersecurity strategy blends human diligence with proactive technological support from an expert Anaheim IT partner who can manage the complex tools that act as a safety net.
- The goal isn’t to eliminate human error entirely, but to create a resilient organization where employees can confidently identify, report, and help stop threats before they cause damage.
The Human Factor: Why Your Employees Are Cybercriminals’ #1 Target
Why are well-meaning employees the biggest risk to your business’s security? The answer is simple: they hold the keys to the kingdom. They have legitimate access to sensitive data, financial accounts, and critical systems. Cybercriminals know that it’s often easier to trick a person into opening a door than it is to break that door down.
This is the foundation of social engineering—a strategy that relies on psychological manipulation rather than pure technical exploits. Attackers prey on human nature: our trust, our desire to be helpful, and our fear of getting in trouble. A convincing email that appears to be from a senior executive or a trusted vendor can be all it takes to bypass even the most sophisticated security software.
The statistics paint a stark picture. A recent report found that human error contributed to 95% of data breaches in 2024, driven by simple mistakes like clicking malicious links, using weak passwords, or falling for phishing scams. The stakes for your Anaheim business are immense. According to Forbes, the average cost of a data breach has soared to $4.88 million, a cost that can be devastating for any small or medium-sized business.
From Liability to Asset: Building Your Human Firewall Strategically
It’s time to shift your perspective. Stop viewing your employees as an unavoidable liability and start seeing them as a potential security powerhouse. This is the core concept behind building a “human firewall”—an organization-wide culture of security awareness where every single employee is an active participant in your defense system.
A human firewall isn’t built by accident or with a single, uninspired training session. It requires a deliberate and comprehensive strategy that embeds security into the fabric of your company’s operations. This isn’t about blaming individuals for mistakes; it’s about empowering them with the knowledge and tools to make better decisions.
Recognizing that your employees are the primary target for cybercriminals is a critical first step. But building a resilient, employee-focused security framework requires more than awareness—it takes a strategy informed by professional insight. IT consulting in Anaheim can guide businesses through this process, helping identify hidden vulnerabilities, implement the right safeguards, and ensure your team is prepared to respond effectively to threats. A key part of this is getting a thorough assessment of your IT environment to uncover risks and lay the groundwork for a robust, long-term security plan.
See also: Smart Tech: How to Create a Safer Home Office
The 3 Pillars of an Employee-Centric Security Program
A strong human firewall is built on three foundational pillars. Each one addresses a different aspect of employee behavior and organizational culture, working together to create a multi-layered, human-centric defense.
Pillar 1: Establish a Clear and Simple Cybersecurity Policy
Before you can train your team, you need to define the rules of the road. A cybersecurity policy shouldn’t be a dense, 50-page legal document that no one reads. It should be a practical guide that is clear, concise, and easy for non-technical employees to understand and follow. It serves as the foundation for all your security efforts.
Your policy should clearly outline expectations and procedures. Key components to include are:
- Acceptable Use: Rules for using company devices, networks, and software. This includes guidance on connecting to public Wi-Fi and using personal devices for work.
- Password Management: Requirements for creating strong, unique passwords, rules for changing them, and a strict policy against sharing credentials.
- Data Handling: Guidelines on how to store, share, and dispose of sensitive company and customer information.
- Incident Reporting: A simple, clear process for what to do if an employee suspects a security issue, clicks a suspicious link, or receives a phishing email.
Most importantly, this policy must be accessible. Store it in a shared, easy-to-find location and communicate its key points regularly during team meetings and onboarding to ensure it stays top of mind.
Pillar 2: Implement Comprehensive and Ongoing Security Training
A single security training session during onboarding is not enough to combat the ever-evolving landscape of cyber threats. Effective security education must be a continuous process that keeps your team prepared for the real-world tactics they will face.
Your training program should focus on the most common threats targeting employees. These include phishing, social engineering, malware, and credential theft. Given that around 90% of all cyberattacks start with a phishing email, this should be your number one training priority. Teach your team to spot the red flags: suspicious sender addresses, urgent or threatening language, unexpected attachments, and links that don’t match their supposed destination.
To make the knowledge stick, training needs to be engaging. Move beyond dry presentations and use interactive formats like videos, quizzes, and workshops. Use real-world examples of phishing emails and social engineering scams to make the threats tangible and memorable for your team.
Pillar 3: Test, Reinforce, and Foster a Positive Security Culture
A policy and training program are only effective if they are put into practice and reinforced over time. This third pillar is about turning security knowledge into a daily habit and building a culture where everyone feels responsible for protecting the organization.
One of the most effective ways to do this is through controlled phishing simulations. These are fake phishing emails sent by your IT team or partner to your employees to safely test their awareness. The results aren’t for punishing anyone; they are for identifying knowledge gaps and providing targeted, just-in-time retraining to those who need it most.
Crucially, you must foster a blame-free incident reporting culture. Employees must feel safe reporting a mistake, like clicking a suspicious link, without fear of punishment. When someone reports an incident, thank them for their vigilance. This positive reinforcement encourages proactive reporting and allows your IT team to respond to potential threats much faster. Ultimately, security must be championed from the top down. When leadership makes security a visible priority, it becomes a shared responsibility across the entire company.
How Technology Supports Your Human Firewall
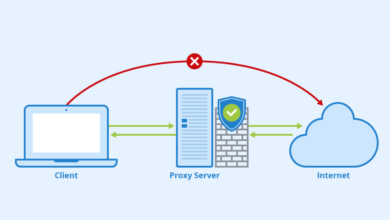
A strong security culture doesn’t replace the need for technology; it enhances its effectiveness. Think of technology as the safety net that catches the mistakes your human firewall might miss. When your people and your technology work in harmony, your overall security posture becomes exponentially stronger.
Several key technologies are essential for reinforcing your human firewall:
- Advanced Email Filtering: This service automatically scans incoming emails to block spam, viruses, and known phishing attacks before they ever reach an employee’s inbox.
- Multi-Factor Authentication (MFA): MFA requires a second form of verification (like a code from a mobile app) in addition to a password. This provides a critical layer of protection against stolen credentials.
- Endpoint Protection: This goes beyond traditional antivirus software to protect laptops, desktops, and mobile devices from sophisticated malware and other advanced threats.
The role of a proactive IT consultant expert is to manage these complex technologies, ensuring they are configured correctly, monitored constantly, and kept up-to-date. A Managed IT or Cybersecurity service acts as the support system for your human firewall, handling the technical heavy lifting so you can focus on building a strong policy, delivering effective training, and fostering a resilient security culture.
Conclusion: Your Strongest Defense Is an Empowered Team
The link between employee behavior and your business’s security is undeniable. While technology provides a vital shield, the human element remains the most dynamic and critical variable in your defense strategy. Cybercriminals will always target your people because they are often the easiest path to your data.
But this doesn’t have to be a source of fear. By adopting a proactive approach built on clear policies, continuous training by Anaheim IT consultants, and a supportive, security-first culture, you can mitigate human risk and transform your team into a powerful security asset.
Investing in your people’s security awareness is not just an IT expense. It’s a strategic investment in the resilience, continuity, and long-term success of your entire business. An empowered, educated, and vigilant team is, and always will be, your strongest defense.