Insider Threats in Finance: Not Just Employees, But Systems Too

In the world of finance, a security breach is more than an inconvenience; it’s a direct threat to the bottom line and client trust. The stakes are extraordinarily high, with the average cost of a data breach for a financial services firm in 2024 reaching nearly $6.1 million. For decades, the term “insider threat” conjured images of a disgruntled employee smuggling out client lists. While that danger remains very real, a more subtle and pervasive threat is growing from within your own technology infrastructure.
Firms are rightly focused on human behavior, but they often overlook the vulnerabilities lurking in their own networks, cloud services, and legacy applications. These systems can be compromised or misconfigured to act as internal threat vectors, silently exfiltrating data or creating backdoors for external attacks. To truly secure a modern financial firm, leaders must expand their definition of an “insider threat” to include the very technology that powers their business.
Key Takeaways
- The definition of an insider threat now includes not only malicious or negligent employees but also compromised systems, misconfigured cloud assets, and vulnerable legacy technology.
- Financial firms are a top target due to the high value of their data, and legacy systems significantly increase their attack surface for these new types of internal threats.
- An effective modern defense strategy is built on three pillars: Proactive Governance, advanced technology (like AI/ML), and a strong security-aware culture.
- Shifting from a reactive to a proactive security posture requires specialized managed IT expertise to handle the complexities of both human and system-based risks.
The Evolving Threat Landscape: Beyond the Malicious Employee
The classic idea of an insider threat is simple, but the modern reality is far more complex. To build an effective defense, you must first understand the full spectrum of risks, which now extends far beyond human intent to include the state of your technology itself.
The Three Faces of the Human Insider
Before exploring the new technological insiders, it’s essential to ground our understanding in the three traditional profiles of human threats. These remain a significant concern, with 30% of all data breaches caused by an insider threat, according to one Verizon report.
- The Malicious Insider: This is the classic threat actor—a disgruntled or greedy employee who intentionally steals data like client lists, proprietary algorithms, or trade secrets for personal or financial gain.
- The Accidental or Negligent Insider: More common and often just as damaging, this is the well-meaning employee who unintentionally exposes data. This can happen by falling for a phishing scam, sharing sensitive information in an unsecure manner, or simply making a human error.
- The Compromised Insider: This occurs when an employee’s credentials are stolen by an external attacker through methods like phishing or malware. The attacker then masquerades as a legitimate user, gaining trusted access to the network and its resources.
See also: Smart Tech: How to Create a Safer Home Office
The New Insider: When Your Systems and Network Go Rogue
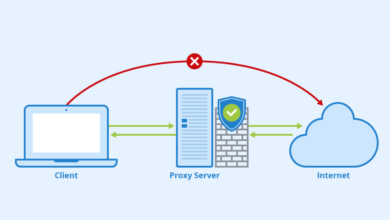
Here is where the definition of an insider threat must expand. A “system insider threat” happens when a part of your own IT infrastructure—a network device, a cloud service, or an application—is vulnerable or misconfigured, creating an internal pathway for data exfiltration or system compromise. It behaves like a malicious insider, but without human intent.
Consider these concrete examples:
- An unpatched server on your network contains a known vulnerability that allows an attacker who has already breached the perimeter to move laterally and access sensitive databases.
- A cloud storage bucket containing confidential client documents is accidentally configured with public permissions, making it accessible to anyone on the internet.
- An automated data-processing script is given overly broad access permissions, allowing it to read and write to databases it has no business function to access.
This problem is directly linked to the pressures of digital transformation and the persistence of aging infrastructure. As firms adopt new cloud technologies while maintaining legacy systems, their technology environment becomes more complex and harder to secure. This complexity creates gaps. In fact, organizations relying on legacy systems have experienced a 40 percent surge in insider risk incidents in recent years. These system-based threats operate silently and are often missed by security tools designed only to monitor suspicious user behavior.
Addressing these silent system vulnerabilities often starts with a comprehensive approach to technology oversight. Firms that adopt managed IT services for finance firms gain a layer of continuous monitoring and proactive management across both legacy and cloud environments. By keeping configurations up to date, applying security best practices, and streamlining network oversight, these services reduce the risk of unnoticed gaps while letting internal teams focus on core financial operations. It’s less about a vendor stepping in and more about embedding consistent expertise that anticipates weaknesses before they become incidents.
Confronting a Complex Problem Requires a Strategic Partner
Protecting a financial firm now means defending against a two-front war: one against human error and malice, and another against your own network’s vulnerabilities. This new reality demands a sophisticated, multi-layered security strategy that addresses both people and platforms.
For many financial leaders, developing and maintaining the deep in-house expertise needed to manage this dual threat is a significant operational and financial challenge. It requires specialists in network architecture, cloud security, threat intelligence, and compliance. This is why many firms choose to partner with industry specialists for cybersecurity. This approach provides immediate access to high-level strategic guidance, like a virtual CISO (vCISO), alongside the technical teams needed to manage complex network and cloud security—all without the overhead of building a large internal department.
Building a Modern Defense: A Three-Pillar Strategy for Insider Threat Prevention
A modern, effective insider threat program cannot be a patchwork of tools and policies. It must be a holistic strategy built on three interconnected pillars: Proactive Governance, Advanced Technology, and a strong Security Culture. These pillars work together to create overlapping layers of defense, ensuring that a failure in one area is caught by another.
This three-pillar framework is more than a security blueprint; it’s a business case. It provides the structure needed to satisfy regulators, protect your firm’s reputation, and demonstrate due diligence to your board of directors.
- Governance: This is the foundation—the rules, policies, and oversight that define how data is handled and who can access it.
- Technology: These are the tools that monitor, detect, and respond to threats in real-time, watching both users and systems.
- Culture: This is the human element—the shared understanding and commitment to security that turns every employee into a defender.
Conclusion: Shifting from Reactive Defense to Proactive Resilience
The landscape of insider threats has irrevocably changed. The most resilient financial firms are those that recognize danger can originate not just from people with bad intentions or careless habits, but from the very systems they rely on every day. A misconfigured cloud asset or a vulnerable legacy server can be just as damaging as a malicious employee.
By building a defense on the three pillars of Proactive Governance, Advanced Technology, and a strong Security Culture with the help of financial institution-managed IT experts, you create a comprehensive framework for managing this modern risk. This integrated approach allows you to satisfy regulators, protect your assets, and maintain the trust you have worked so hard to build with your clients.
Ultimately, this shift in perspective is about moving from a reactive defensive posture to one of proactive organizational resilience. By expanding your definition of an insider and partnering with the right experts to manage the complexity, you can transform your insider threat program from a defensive necessity into a true strategic advantage.