Strategies to Manage Container Image Security

Managing container image integrity involves different kinds of strategies. Protect images from cyber threats by implementing regular updates. Include images from trusted libraries and adopt a proactive approach to counter cyber attacks. For containerization security, do regular vulnerability scanning in the container environment. Necessary to implement image signing verification strategies to stop unwanted access to your containerized environment.
Strategies to Manage Container Images:
There are certain strategies to manage container images; here, we discern the most important of them.
Using Trusted Base Images:
To secure the container environment, allow only images from verified and reputable registries to avoid vulnerabilities. Make a strategy to regularly scan for common vulnerabilities in the container images. You can scan container images for security flaws and outdated dependencies. For example, containerization security uses digital signatures. Try to ensure container images are tamper-proof and taken from trusted sources.
See also: Top Garage Storage System Ideas for Every Home
Keep Up With Updates:
Software companies may sometimes issue a security threat to their software. Monitoring and logging container activity and continuously tracking container behaviors for different kinds of softwares updates. Follow the instructions or security alerts issued by a software company. When you update containerization security regularly then you can avoid major security threats.
Principle of Least Privilege:
For better image security, it is necessary to restrict container permissions. The least privilege principle makes sure to limit potential security risks. For image security, enforce secure configuration management on different images. Being a business, apply the industry standards and best practices to prevent misconfigurations of different softwares. Apply a strategy of keeping updated and patch images to eliminate known vulnerabilities.
Secure Your Mobile Device:
Securing apps and networks isn’t the only thing for containerization security. Secure your mobile phone. Use a strong password and biometric features, and ensure you have disabled your WiFi or Bluetooth; never connect to a public WiFi automatically. Download things with precautionary measures to ensure container image security.
Beware Of Social Engineering:
Don’t share WhatsApp numbers or contact numbers on social media openly. Beware that hackers may also contact you; this kind of attack may not be on your system, but hackers find different ways to dupe containerization security.
Use Security Software:
These days, storage doesn’t cost you a lot, so it’s not an excuse that you haven’t created a backup for your important data. Security softwares is a good way to implement container image integrity. The security software, such as anti-spyware, anti-malware, and anti-virus programs, protects the system from known viruses. Detect and remove malicious code before it is going to harm your system.
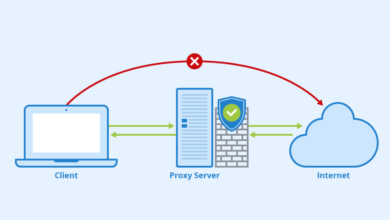
Put Up A Firewall:
A firewall acts like a gatekeeper between your container images and data. A firewall is a major barrier to prevent cyber-attacks. Try to update your firewall regularly and make sure you have installed the latest version. Otherwise, they may not be fully effective.
Conclusion:
Organizations can effectively manage containerization security by implementing these strategies. Protect their infrastructure from potential cyber risks. Businesses do need to adopt an approach of proactive security measures, not reactive after damage.