Account & Call Log Validation – courtneymacneil1, 8096830290, 728362970, 7806661470, 7207120300, 7028778116, panarasss8, Tuzofalotaniz, Hexcisfesasjiz, 886279325026
Account & Call Log Validation examines the integrity of identities and numbers linked to the listed accounts and identifiers. It applies cross-device checks, document-based reconciliation, and audit-ready trails to ensure traceable activity. Discrepancies are flagged for stepwise investigation, with emphasis on privacy-preserving corroboration and consistent records. The framework supports accountability and user-centric validation, but questions remain about how these controls scale and adapt across varied use cases and compliance requirements.
What Is Account & Call Log Validation and Why It Matters
Account and call log validation is the process of verifying the accuracy, completeness, and integrity of user accounts and their associated telephone activity. It establishes reliable data trails for audits and compliance, reducing error risk. The practice emphasizes consistent procedures, traceable records, and repeatable checks.
Key outcomes include enhanced reliability, accountability, and trust in system interactions, through rigorous account validation and call validation.
Verifying Identities and Numbers: Cross-Checks Across Devices
Cross-device verification of identities and numbers involves methodically matching user credentials and telephone identifiers across multiple platforms and hardware. The process addresses verification challenges by aligning device IDs, SIM traces, and account aliases, while preserving privacy.
Rigorous cross device corroboration ensures consistency, minimizes spoofed access, and supports authorization workflows without overreach, enabling trusted, user-centric validation across ecosystems.
Spotting Discrepancies: Common Red Flags and How to Investigate
Discrepancies between records often manifest as mismatches in timestamps, geolocation signals, or contact metadata, prompting a targeted, stepwise investigation. Analysts compare event logs, corroborate with external records, and document deviations.
Key actions include identities verification checks and device cross checks, assessing authentication trails, cross-referencing call signatures, and flagging inconsistent metadata for containment while preserving evidentiary integrity.
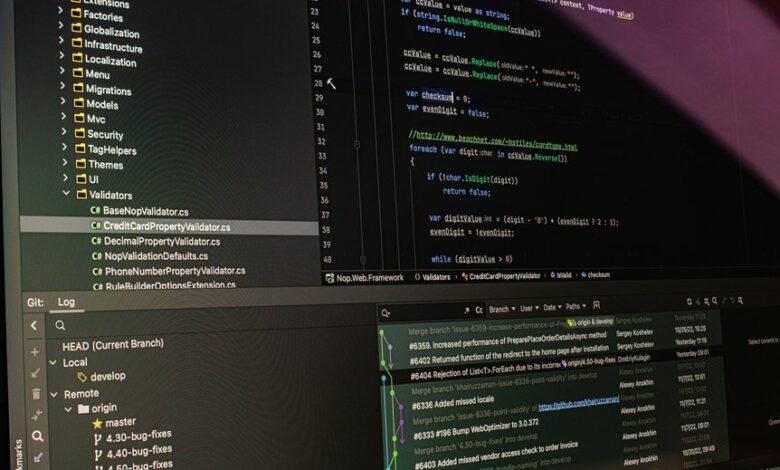
Practical Validation Workflow: Steps, Tools, and Best Practices
Practical validation workflows begin with a structured, repeatable sequence designed to quickly establish data integrity and traceability. A pragmatic validation workflow outlines steps: data collection, normalization, cross-checks, and reconciliation; selecting tools for automation, auditing, and versioning; and establishing identity verification checkpoints.
Documentation, risk assessment, and continuous improvement ensure clarity, reproducibility, and freedom to adapt while maintaining rigorous standards.
Conclusion
In conclusion, the validation process reveals how closely aligned identity, device fingerprints, and call logs must be to sustain trust. When coincidences emerge—names matching numbers, timelines syncing across apps—they echo a pattern of consistency rather than chance. This methodical alignment reinforces accountability: each corroborating detail strengthens the record, while discrepancies prompt targeted investigation. The resulting certainty is not happenstance, but a deliberate convergence of data points guiding auditable, privacy-preserving validation.







