User Data Verification Batch – Baengstezic, annalizababy10, heimvinec6025, 655cf838c4da2, Vl s9zelo-Dofoz, Jivozvotanis, zozxodivnot2234, e5b1h1k, 84862252416, Buntrigyoz
The User Data Verification Batch, led by Baengstezic and colleagues, represents a structured approach to validating user-provided information. It combines automated checks with human review to balance speed and accuracy. Privacy safeguards and audit trails are central, with emphasis on compliance and risk scoring. The process aims for consistent cross-source validation and actionable outcomes for governance and experimentation. Stakeholders are invited to consider the tradeoffs and implications as they weigh implementation and oversight.
What Is the User Data Verification Batch and Why It Matters
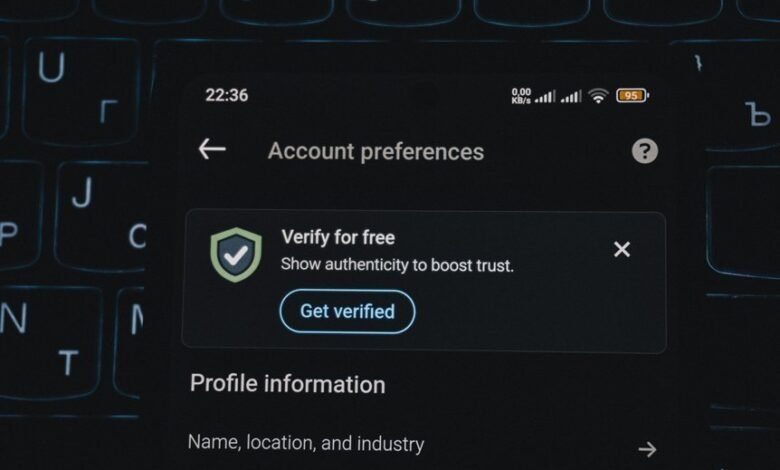
The User Data Verification Batch refers to a structured process by which organizations review and confirm the accuracy, completeness, and integrity of user-provided data before it is used for decisions, onboarding, or downstream analytics. It emphasizes privacy safeguards, clear verification interpretation, and reliable identity checks, while outlining rigorous data handling practices to minimize risk and ensure auditable, compliant outcomes.
How Baengstezic and Co. Streamline Identity Checks
Baengstezic and Co. employ a structured, risk-aware approach to identity checks, integrating automated verification with manual review to ensure consistency across data sources. This hybrid workflow enhances onboarding efficiency while maintaining privacy safeguards and data ethics. Compliance standards guide parameter tuning, reducing false positives. The process prioritizes auditable decisions, transparently documenting risk scores and reviewer notes for accountable verification.
Privacy Safeguards and Compliance in the Verification Process
Privacy safeguards and compliance verification are monitored via independent audits, policy alignment, and risk assessment to deter improper use.
Practical Use Cases and How to Interpret Verification Results
How can verification results be translated into actionable insights for operations and governance, and what do these outcomes imply for decision-makers? Verification outcomes inform data quality improvements, prioritize risk assessment actions, and guide policy adjustments. Clear audit trails support accountability, while respecting user consent. Interpretations enable targeted governance changes, robust monitoring, and measured experimentation, balancing freedom with safeguards and measurable performance indicators.
Conclusion
In sum, the User Data Verification Batch operates as a disciplined lens, filtering ambiguity from streams of identity. It blends automated scrutineering with measured human review, ensuring consistency while safeguarding privacy. The resulting risk scores act as compass bearings, guiding governance and experimentation with caution. Like a well-tuned clock, the system balances speed and accuracy, illuminating data trails without overspill, and leaving stakeholders with auditable, ethically grounded confidence.







